Can you please explain the significance of the JQuery@3.3.1 vulnerability and why it’s crucial to upgrade my system?
Check all explanations here

Here’s a clear explanation of the security issues around jQuery 3.3.1, why they matter, and why upgrading your system is important:
What’s Vulnerable in jQuery 3.3.1
Although it might seem recent, jQuery 3.3.1 has known security vulnerabilities that are documented and have been widely reported by security scanners and advisory services. These include: (VulnInfoGuide)
1. Cross-Site Scripting (XSS) Vulnerabilities
- In affected versions (including 3.3.1), passing HTML — even sanitized HTML — into DOM-manipulation functions like
.html(),.append(),.prepend(), etc., can still execute untrusted code. (VulnInfoGuide) - Specific CVEs include CVE-2020-11022 and CVE-2020-11023, which are medium-severity XSS issues (CVSS ~6.1) that are fixed in jQuery 3.5.0. (cyber.vumetric.com)
2. Prototype Pollution
- Versions below 3.4.0 (including 3.3.1) are vulnerable to prototype pollution in
jQuery.extend(). This lets an attacker inject or modify object properties that then affect all JavaScript objects, which can lead to XSS or logic issues down the line. (VulnInfoGuide)
Confirmed Vulnerabilities
A vulnerability scan (e.g., Snyk reports) lists multiple findings against jQuery 3.3.1 (CVE-2020-23064, CVE-2020-11023, CVE-2020-11022, CVE-2019-11358), and all of these are fixed in newer jQuery releases. (GitHub)
Why These Vulnerabilities Matter
1. Security Exploits Are Real
Even if you don’t see a public exploit for your exact use case, the vulnerabilities are well-documented and scanners correctly flag them because:
- XSS allows injection of malicious JavaScript, which can steal session tokens, capture user data, or perform actions as the user.
- Prototype pollution can undermine the foundational assumptions of your application’s runtime behavior. (VulnInfoGuide)
In other words: a determined attacker can find a way to abuse these issues if your app uses vulnerable code in contexts where user input interacts with jQuery. (cyber.vumetric.com)
2. External Scans & Compliance
- Security scans (e.g., vulnerability scanners, compliance tools, PCI/DSS tests) will mark your system as non-compliant if known vulnerabilities are present.
- Many regulatory frameworks require patching known vulnerabilities promptly, and outdated third-party libraries like jQuery are often flagged. (blog.jquery.com)
This affects both internal risk management and external audits.
3. Broad Impact
jQuery is one of the most widely used JavaScript libraries, and older versions are extremely common — which means attackers are familiar with the weaknesses and how to exploit them. (blog.jquery.com)
Why You Should Upgrade
1. Security Patches
Upgrading to at least jQuery 3.5.0 or later:
- Eliminates the XSS issues fixed by CVE-2020-11022 and CVE-2020-11023. (cyber.vumetric.com)
- Removes the prototype pollution weakness fixed in versions = 3.4.0. (VulnInfoGuide)
Newer jQuery versions also implement improved security practices by default. (blog.jquery.com)
2. Better Browser Support & Maintenance
-
Older versions aren’t maintained, meaning no future security fixes. (blog.jquery.com)
-
By upgrading, you reduce risk and stay current with modern browser environments and best practices. (blog.jquery.com)
Bottom Line
Using jQuery 3.3.1 puts your application at a known security risk that attackers can exploit through XSS or prototype pollution, especially in real-user contexts or applications that process any user-controlled content. (VulnInfoGuide)
Upgrading to a fixed version (3.5.0 or later) is important because it:
- Closes known security flaws
- Helps your app pass scans and compliance checks
- Lowers your exposure to common attack vectors
Related articles
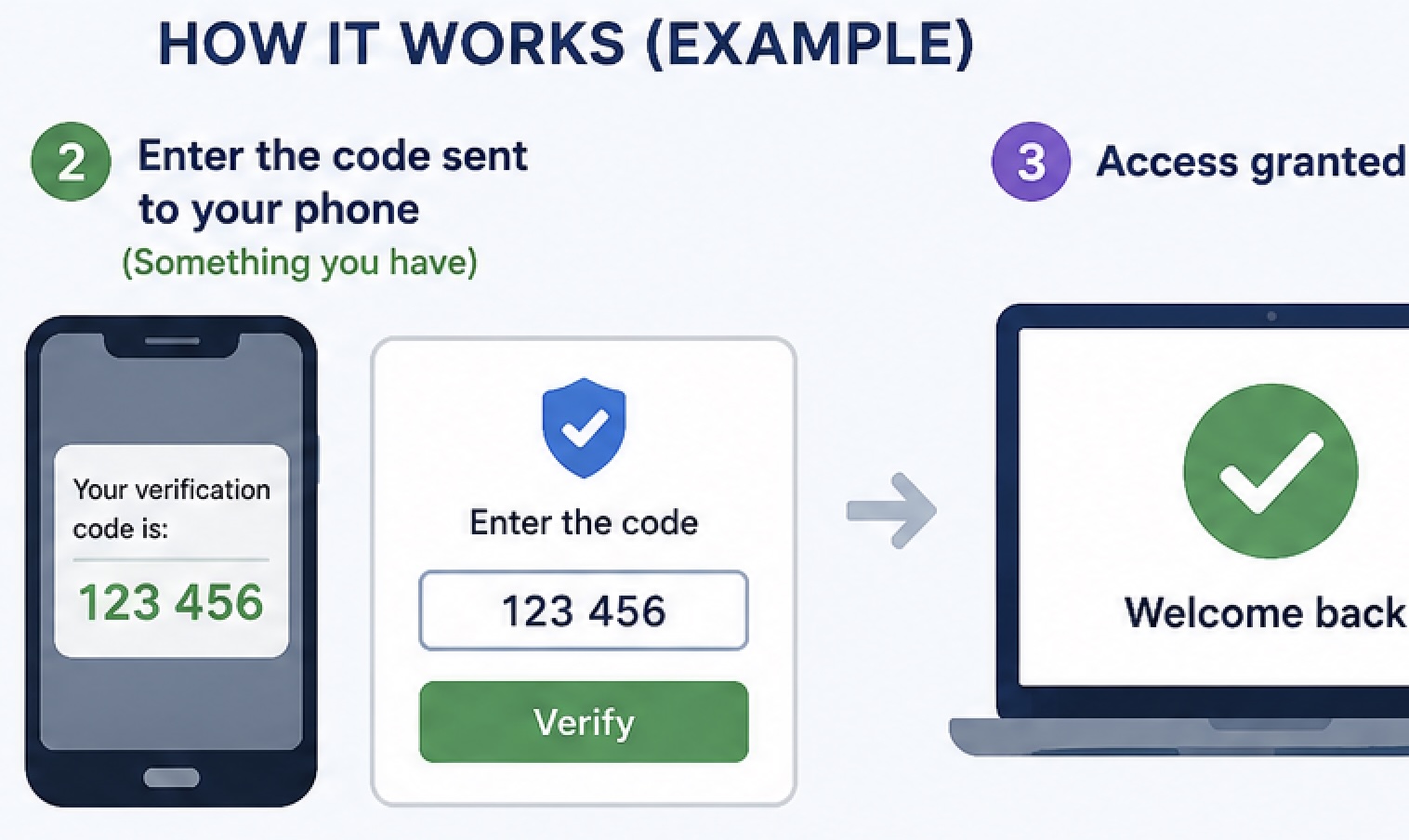
What is multi-factor authentication?
Multi-factor authentication (often called MFA)...
Your Reward Points Are Expiring
Recent warnings from the Federal Trade Commission
The scam offer
You receive a text message claiming that you can..
The most commonly used passwords in 2025 and 2026
The most commonly used (and easily hacked) pass...
Can you please tell me where I can check the security headers of my website? Also, why is it crucial to have an A+ rating
Checking your website’s security headers is pretty
Generate TOTP authentication and validate
To generate a QR code for a Time-Based One-Time
AI-Powered Hacking: Automated Exploits
What is it? How to protect myself
What exactly is a content security policy, and how can I incorporate it into my website
Try to understand and follow
Why upgrading and auditing the APIs used in your software or SaaS is extremely important?
Check all options here for you
Phishing Campaign Targets WhatsApp Accounts
Researchers at Gen Digital Inc. (a global cybersec

 Mauricio Junior
Mauricio Junior